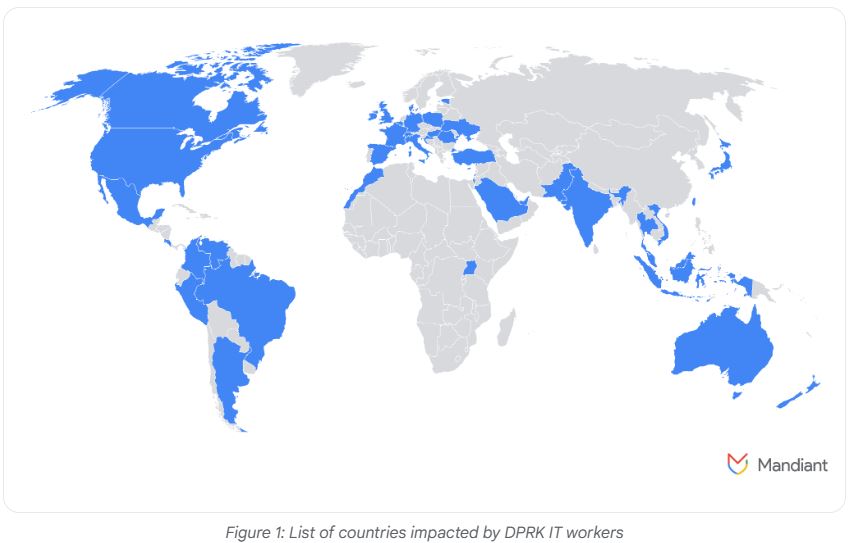
Fraudulent technology professionals linked to North Korea are broadening their infiltration efforts to blockchain companies outside the United States in light of heightened scrutiny from officials. Some have already embedded themselves within crypto initiatives in the UK, according to a report.
A member of the Threat Intelligence Group highlighted that, while the US remains a significant target, increased awareness and challenges related to employment verification have compelled North Korean tech workers to seek positions in firms located beyond US borders.
“As a reaction to growing awareness of the risks in the United States, they have developed a global network of fraudulent identities to improve their operational flexibility,” the advisor noted.
“The identification of facilitators in the UK indicates a swift establishment of a worldwide framework and support system that enables their ongoing activities,” he added.
The Threat Intelligence Group reports an expansion of North Korean tech workers’ operations amidst rising US enforcement.
These North Korea-linked workers are infiltrating a variety of projects, from traditional web development to sophisticated blockchain applications, including initiatives involving Solana and Anchor smart contracts.
Additionally, another project focused on creating a blockchain-based job marketplace, along with an AI web application utilizing blockchain technology, was discovered to have North Korean personnel involved.
“These individuals pose as legitimate remote employees to infiltrate companies and generate funds for the regime,” the advisor noted.
“This exposes organizations hiring DPRK IT workers to potential espionage, data theft, and operational disruption.”
North Korea Turning to Europe for Tech Employment
In addition to the UK, there is a notable emphasis on Europe, with one worker reportedly utilizing at least 12 different personas across the continent, while others have furnished resumes claiming degrees from Belgrade University in Serbia and residency in Slovakia.
Separate investigations have located personas targeting job opportunities in Germany and Portugal, as well as login details for user accounts on European job portals, guidance for navigating European employment sites, and a broker specializing in counterfeit passports.
Since late October, North Korean workers have also escalated their extortion efforts, targeting larger organizations. Analysts suggest that these workers may feel pressure to sustain revenue streams as law enforcement actions intensify within the US.
“In several instances, IT workers who were recently terminated threatened to disclose sensitive information from their former employers or to share it with competitors. This information included proprietary materials and source codes for internal projects,” the advisor stated.
Related: North Korean cryptocurrency attacks becoming increasingly sophisticated — Industry analysis
Earlier in the year, the US Justice Department charged two individuals from North Korea with their involvement in a deceptive IT employment scheme affecting at least 64 US companies from April 2018 to August 2024.
Furthermore, the US Treasury’s Office of Foreign Assets Control placed sanctions on entities it attributed as fronts for North Korea, generating revenue via remote IT operations.
Crypto founders have reported an uptick in activity from North Korean hackers, with at least three founders mentioning on March 13 that they thwarted attempts to pilfer sensitive data through phony Zoom calls.
Experiencing audio issues during your Zoom meeting? That’s not a venture capitalist, it’s North Korean hackers.
Fortunately, this founder recognized the situation.
The call initially included a few “VCs” who chatted about audio problems, suggesting there was an… pic.twitter.com/ZnW8Mtof4F
— Nick Bax.eth (@bax1337) March 11, 2025
In August, a blockchain investigator claimed to have uncovered an intricate network of North Korean developers making around $500,000 each month while working for well-known crypto projects.
Magazine: Lazarus Group’s preferred exploit among Crypto hacks analyzed