Tech workers with connections to North Korea are broadening their infiltration efforts into blockchain companies outside the United States, responding to intensified scrutiny from regulatory bodies. Some have successfully embedded themselves in cryptocurrency projects in the UK, according to findings from a threat intelligence group.
An adviser from this group highlighted in an April report that while the US remains a significant target, growing awareness and challenges related to work eligibility have compelled North Korean IT professionals to seek opportunities with companies beyond US borders.
“In light of the increased recognition of the threat within the United States, they have set up a worldwide network of deceptive identities to enhance their operational flexibility,” the adviser noted.
“The identification of facilitators in the UK indicates a swift evolution towards a global support network that sustains their ongoing activities,” they added.
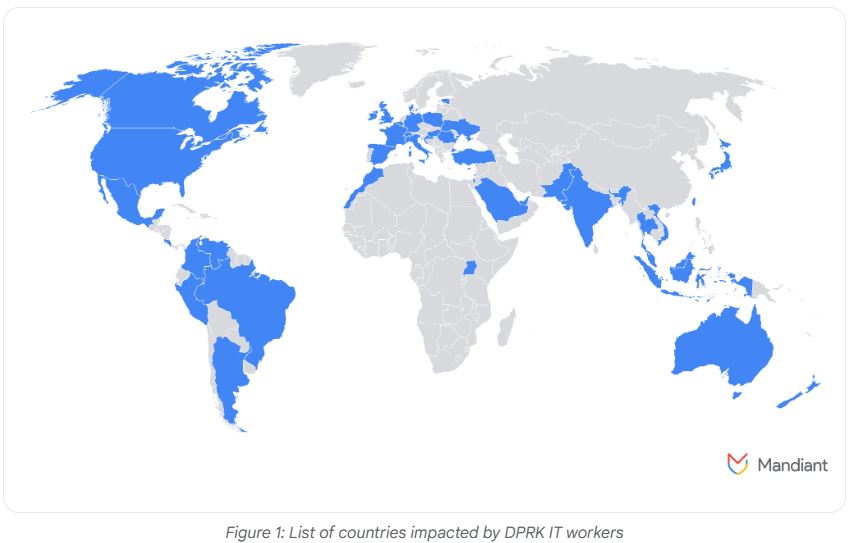
Threat intelligence analysis shows North Korean tech workers extending their reach amid a US crackdown.
The workers associated with North Korea are penetrating various projects, ranging from standard web development to sophisticated blockchain applications, including initiatives related to Solana and smart contract creation with Anchor.
Additionally, a project focused on establishing a blockchain job marketplace and an AI web application that utilizes blockchain technologies has been discovered to involve North Korean personnel.
“These individuals assume the roles of legitimate remote employees to infiltrate firms and generate funds for their regime,” the adviser stated.
“This creates risks of espionage, data theft, and operational disruption for organizations that hire North Korean IT workers.”
North Korea Targets European Tech Job Market
Aside from the UK, there is a significant emphasis on Europe, with one worker employing at least 12 different identities throughout the continent and others claiming qualifications from Belgrade University in Serbia while residing in Slovakia.
Other investigations have uncovered attempts to secure employment in Germany and Portugal, along with access credentials for European job websites, navigational guides for these sites, and the presence of a broker dealing in counterfeit passports.
Additionally, since late October, there’s been a rise in extortion attempts by North Korean workers targeting larger organizations, suggesting these individuals are under pressure to maintain revenue streams amid crackdowns in the US.
“In these situations, IT workers who have recently been terminated have threatened to leak their former employers’ sensitive information or hand it over to competitors, including proprietary data and source code for internal projects,” the adviser explained.
In January, US authorities announced charges against two North Korean nationals for involvement in a fraudulent IT scheme affecting at least 64 US companies over several years.
The US Treasury Department has also imposed sanctions on entities it claims serve as fronts for North Korean operations that generate income through remote IT work schemes.
Meanwhile, crypto entrepreneurs have reported a surge in encounters with North Korean hackers, with at least three founders disclosing on March 13 that they thwarted attempts to pilfer sensitive information through deceptive Zoom calls.
Having audio troubles on your Zoom call? That’s not a venture capitalist; it’s North Korean hackers.
Fortunately, this founder noticed what was happening.
The call begins with a few “VCs” present, who send chat messages indicating they can’t hear you, or suggesting something else is amiss.
In August, a blockchain investigator revealed he had uncovered a sophisticated network of North Korean developers who were reportedly earning $500,000 monthly while working on established cryptocurrency projects.